Exam 15: CompTIA Security+
Question
Question
Question
Question
Question
Question
Question
Question
Question
Question
Question
Question
Question
Question
Question
Question
Question
Question
Question
Question
Question
Question
Question
Question
Question
Question
Question
Question
Question
Question
Question
Question
Question
Question
Question
Question
Question
Question
Question
Question
Question
Question
Question
Question
Question
Question
Question
Question
Question
Question
Question
Question
Question
Question
Question
Question
Question
Question
Question
Question
Question
Question
Question
Question
Question
Question
Question
Question
Question
Question
Question
Question
Question
Question
Question
Question
Question
Question
Question
Question

Unlock Deck
Sign up to unlock the cards in this deck!
Unlock Deck
Unlock Deck
1/1164
Play
Full screen (f)
Exam 15: CompTIA Security+
1
A botnet has hit a popular website with a massive number of GRE-encapsulated packets to perform a DDoS attack. News outlets discover a certain type of refrigerator was exploited and used to send outbound packets to the website that crashed. To which of the following categories does the refrigerator belong?
A) SoC
B) ICS
C) IoT
D) MFD
A) SoC
B) ICS
C) IoT
D) MFD
IoT
2
Refer to the following code: 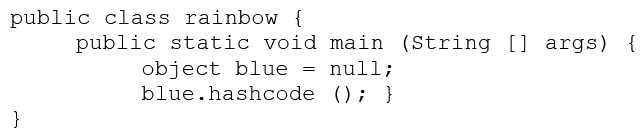 Which of the following vulnerabilities would occur if this is executed?
Which of the following vulnerabilities would occur if this is executed?
A) Page exception
B) Pointer deference
C) NullPointerException
D) Missing null check
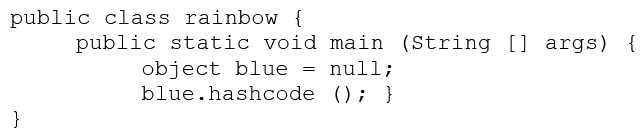 Which of the following vulnerabilities would occur if this is executed?
Which of the following vulnerabilities would occur if this is executed?A) Page exception
B) Pointer deference
C) NullPointerException
D) Missing null check
Missing null check
3
A security analyst is hardening a server with the directory services role installed. The analyst must ensure LDAP traffic cannot be monitored or sniffed and maintains compatibility with LDAP clients. Which of the following should the analyst implement to meet these requirements? (Choose two.)
A) Generate an X.509-compliant certificate that is signed by a trusted CA.
B) Install and configure an SSH tunnel on the LDAP server.
C) Ensure port 389 is open between the clients and the servers using the communication.
D) Ensure port 636 is open between the clients and the servers using the communication.
E) Remote the LDAP directory service role from the server.
A) Generate an X.509-compliant certificate that is signed by a trusted CA.
B) Install and configure an SSH tunnel on the LDAP server.
C) Ensure port 389 is open between the clients and the servers using the communication.
D) Ensure port 636 is open between the clients and the servers using the communication.
E) Remote the LDAP directory service role from the server.
Generate an X.509-compliant certificate that is signed by a trusted CA.
Ensure port 636 is open between the clients and the servers using the communication.
Ensure port 636 is open between the clients and the servers using the communication.
4
A penetration tester is crawling a target website that is available to the public. Which of the following represents the actions the penetration tester is performing?
A) URL hijacking
B) Reconnaissance
C) White box testing
D) Escalation of privilege
A) URL hijacking
B) Reconnaissance
C) White box testing
D) Escalation of privilege

Unlock Deck
Unlock for access to all 1164 flashcards in this deck.
Unlock Deck
k this deck
5
Which of the following threat actors is MOST likely to steal a company's proprietary information to gain a market edge and reduce time to market?
A) Competitor
B) Hacktivist
C) Insider
D) Organized crime.
A) Competitor
B) Hacktivist
C) Insider
D) Organized crime.

Unlock Deck
Unlock for access to all 1164 flashcards in this deck.
Unlock Deck
k this deck
6
Which of the following attacks specifically impact data availability?
A) DDoS
B) Trojan
C) MITM
D) Rootkit
A) DDoS
B) Trojan
C) MITM
D) Rootkit

Unlock Deck
Unlock for access to all 1164 flashcards in this deck.
Unlock Deck
k this deck
7
Users report the following message appears when browsing to the company's secure site: This website cannot be trusted. Which of the following actions should a security analyst take to resolve these messages? (Choose two.)
A) Verify the certificate has not expired on the server.
B) Ensure the certificate has a .pfx extension on the server.
C) Update the root certificate into the client computer certificate store.
D) Install the updated private key on the web server.
E) Have users clear their browsing history and relaunch the session.
A) Verify the certificate has not expired on the server.
B) Ensure the certificate has a .pfx extension on the server.
C) Update the root certificate into the client computer certificate store.
D) Install the updated private key on the web server.
E) Have users clear their browsing history and relaunch the session.

Unlock Deck
Unlock for access to all 1164 flashcards in this deck.
Unlock Deck
k this deck
8
Which of the following characteristics differentiate a rainbow table attack from a brute force attack? (Choose two.)
A) Rainbow table attacks greatly reduce compute cycles at attack time.
B) Rainbow tables must include precomputed hashes.
C) Rainbow table attacks do not require access to hashed passwords.
D) Rainbow table attacks must be performed on the network.
E) Rainbow table attacks bypass maximum failed login restrictions.
A) Rainbow table attacks greatly reduce compute cycles at attack time.
B) Rainbow tables must include precomputed hashes.
C) Rainbow table attacks do not require access to hashed passwords.
D) Rainbow table attacks must be performed on the network.
E) Rainbow table attacks bypass maximum failed login restrictions.

Unlock Deck
Unlock for access to all 1164 flashcards in this deck.
Unlock Deck
k this deck
9
A company is using a mobile device deployment model in which employees use their personal devices for work at their own discretion. Some of the problems the company is encountering include the following: There is no standardization. Employees ask for reimbursement for their devices. Employees do not replace their devices often enough to keep them running efficiently. The company does not have enough control over the devices. Which of the following is a deployment model that would help the company overcome these problems?
A) BYOD
B) VDI
C) COPE
D) CYOD
A) BYOD
B) VDI
C) COPE
D) CYOD

Unlock Deck
Unlock for access to all 1164 flashcards in this deck.
Unlock Deck
k this deck
10
An auditor wants to test the security posture of an organization by running a tool that will display the following: 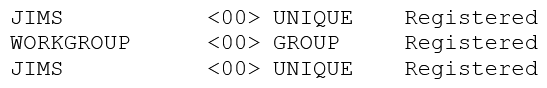 Which of the following commands should be used?
Which of the following commands should be used?
A) nbtstat
B) nc
C) arp
D) ipconfig
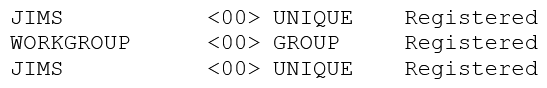 Which of the following commands should be used?
Which of the following commands should be used?A) nbtstat
B) nc
C) arp
D) ipconfig

Unlock Deck
Unlock for access to all 1164 flashcards in this deck.
Unlock Deck
k this deck
11
Which of the following BEST describes an important security advantage yielded by implementing vendor diversity?
A) Sustainability
B) Homogeneity
C) Resiliency
D) Configurability
A) Sustainability
B) Homogeneity
C) Resiliency
D) Configurability

Unlock Deck
Unlock for access to all 1164 flashcards in this deck.
Unlock Deck
k this deck
12
Which of the following types of cloud infrastructures would allow several organizations with similar structures and interests to realize the benefits of shared storage and resources?
A) Private
B) Hybrid
C) Public
D) Community
A) Private
B) Hybrid
C) Public
D) Community

Unlock Deck
Unlock for access to all 1164 flashcards in this deck.
Unlock Deck
k this deck
13
An organization has determined it can tolerate a maximum of three hours of downtime. Which of the following has been specified?
A) RTO
B) RPO
C) MTBF
D) MTTR
A) RTO
B) RPO
C) MTBF
D) MTTR

Unlock Deck
Unlock for access to all 1164 flashcards in this deck.
Unlock Deck
k this deck
14
Which of the following explains why vendors publish MD5 values when they provide software patches for their customers to download over the Internet?
A) The recipient can verify integrity of the software patch.
B) The recipient can verify the authenticity of the site used to download the patch.
C) The recipient can request future updates to the software using the published MD5 value.
D) The recipient can successfully activate the new software patch.
A) The recipient can verify integrity of the software patch.
B) The recipient can verify the authenticity of the site used to download the patch.
C) The recipient can request future updates to the software using the published MD5 value.
D) The recipient can successfully activate the new software patch.

Unlock Deck
Unlock for access to all 1164 flashcards in this deck.
Unlock Deck
k this deck
15
A security analyst is diagnosing an incident in which a system was compromised from an external IP address. The socket identified on the firewall was traced to 207.46.130.0:6666. Which of the following should the security analyst do to determine if the compromised system still has an active connection?
A) tracert
B) netstat
C) ping
D) nslookup
A) tracert
B) netstat
C) ping
D) nslookup

Unlock Deck
Unlock for access to all 1164 flashcards in this deck.
Unlock Deck
k this deck
16
A company determines that it is prohibitively expensive to become compliant with new credit card regulations. Instead, the company decides to purchase insurance to cover the cost of any potential loss. Which of the following is the company doing?
A) Transferring the risk
B) Accepting the risk
C) Avoiding the risk
D) Migrating the risk
A) Transferring the risk
B) Accepting the risk
C) Avoiding the risk
D) Migrating the risk

Unlock Deck
Unlock for access to all 1164 flashcards in this deck.
Unlock Deck
k this deck
17
In a corporation where compute utilization spikes several times a year, the Chief Information Officer (CIO) has requested a cost-effective architecture to handle the variable capacity demand. Which of the following characteristics BEST describes what the CIO has requested?
A) Elasticity
B) Scalability
C) High availability
D) Redundancy
A) Elasticity
B) Scalability
C) High availability
D) Redundancy

Unlock Deck
Unlock for access to all 1164 flashcards in this deck.
Unlock Deck
k this deck
18
Despite having implemented password policies, users continue to set the same weak passwords and reuse old passwords. Which of the following technical controls would help prevent these policy violations? (Choose two.)
A) Password expiration
B) Password length
C) Password complexity
D) Password history
E) Password lockout
A) Password expiration
B) Password length
C) Password complexity
D) Password history
E) Password lockout

Unlock Deck
Unlock for access to all 1164 flashcards in this deck.
Unlock Deck
k this deck
19
A security engineer is configuring a system that requires the X.509 certificate information to be pasted into a form field in Base64 encoded format to import it into the system. Which of the following certificate formats should the engineer use to obtain the information in the required format?
A) PFX
B) PEM
C) DER
D) CER
A) PFX
B) PEM
C) DER
D) CER

Unlock Deck
Unlock for access to all 1164 flashcards in this deck.
Unlock Deck
k this deck
20
Which of the following best describes routine in which semicolons, dashes, quotes, and commas are removed from a string?
A) Error handling to protect against program exploitation
B) Exception handling to protect against XSRF attacks.
C) Input validation to protect against SQL injection.
D) Padding to protect against string buffer overflows.
A) Error handling to protect against program exploitation
B) Exception handling to protect against XSRF attacks.
C) Input validation to protect against SQL injection.
D) Padding to protect against string buffer overflows.

Unlock Deck
Unlock for access to all 1164 flashcards in this deck.
Unlock Deck
k this deck
21
A security administrator is developing controls for creating audit trails and tracking if a PHI data breach is to occur. The administrator has been given the following requirements: All access must be correlated to a user account. All user accounts must be assigned to a single individual. User access to the PHI data must be recorded. Anomalies in PHI data access must be reported. Logs and records cannot be deleted or modified. Which of the following should the administrator implement to meet the above requirements? (Choose three.)
A) Eliminate shared accounts.
B) Create a standard naming convention for accounts.
C) Implement usage auditing and review.
D) Enable account lockout thresholds.
E) Copy logs in real time to a secured WORM drive.
F) Implement time-of-day restrictions.
G) Perform regular permission audits and reviews.
A) Eliminate shared accounts.
B) Create a standard naming convention for accounts.
C) Implement usage auditing and review.
D) Enable account lockout thresholds.
E) Copy logs in real time to a secured WORM drive.
F) Implement time-of-day restrictions.
G) Perform regular permission audits and reviews.

Unlock Deck
Unlock for access to all 1164 flashcards in this deck.
Unlock Deck
k this deck
22
Malicious traffic from an internal network has been detected on an unauthorized port on an application server. Which of the following network-based security controls should the engineer consider implementing?
A) ACLs
B) HIPS
C) NAT
D) MAC filtering
A) ACLs
B) HIPS
C) NAT
D) MAC filtering

Unlock Deck
Unlock for access to all 1164 flashcards in this deck.
Unlock Deck
k this deck
23
A high-security defense installation recently begun utilizing large guard dogs that bark very loudly and excitedly at the slightest provocation. Which of the following types of controls does this BEST describe?
A) Deterrent
B) Preventive
C) Detective
D) Compensating
A) Deterrent
B) Preventive
C) Detective
D) Compensating

Unlock Deck
Unlock for access to all 1164 flashcards in this deck.
Unlock Deck
k this deck
24
A company's user lockout policy is enabled after five unsuccessful login attempts. The help desk notices a user is repeatedly locked out over the course of a workweek. Upon contacting the user, the help desk discovers the user is on vacation and does not have network access. Which of the following types of attacks are MOST likely occurring? (Select two.)
A) Replay
B) Rainbow tables
C) Brute force
D) Pass the hash
E) Dictionary
A) Replay
B) Rainbow tables
C) Brute force
D) Pass the hash
E) Dictionary

Unlock Deck
Unlock for access to all 1164 flashcards in this deck.
Unlock Deck
k this deck
25
When configuring settings in a mandatory access control environment, which of the following specifies the subjects that can access specific data objects?
A) Owner
B) System
C) Administrator
D) User
A) Owner
B) System
C) Administrator
D) User

Unlock Deck
Unlock for access to all 1164 flashcards in this deck.
Unlock Deck
k this deck
26
A company has a data classification system with definitions for "Private" and "Public". The company's security policy outlines how data should be protected based on type. The company recently added the data type "Proprietary". Which of the following is the MOST likely reason the company added this data type?
A) Reduced cost
B) More searchable data
C) Better data classification
D) Expanded authority of the privacy officer
A) Reduced cost
B) More searchable data
C) Better data classification
D) Expanded authority of the privacy officer

Unlock Deck
Unlock for access to all 1164 flashcards in this deck.
Unlock Deck
k this deck
27
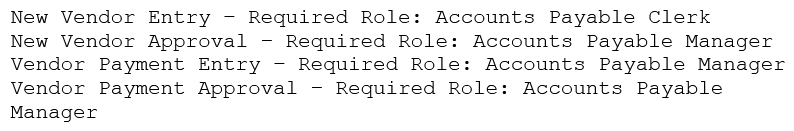
An organization's internal auditor discovers that large sums of money have recently been paid to a vendor that management does not recognize. The IT security department is asked to investigate the organizations the organization's ERP system to determine how the accounts payable module has been used to make these vendor payments. The IT security department finds the following security configuration for the accounts payable module: New Vendor Entry - Required Role: Accounts Payable Clerk New Vendor Approval - Required Role: Accounts Payable Clerk Vendor Payment Entry - Required Role: Accounts Payable Clerk Vendor Payment Approval - Required Role: Accounts Payable Manager Which of the following changes to the security configuration of the accounts payable module would BEST mitigate the risk?
A)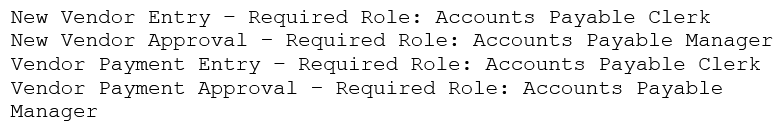
B)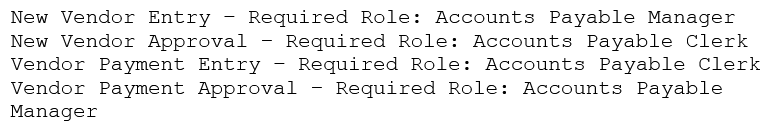
C)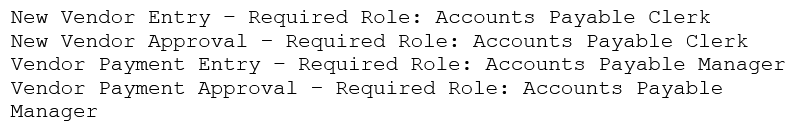
D)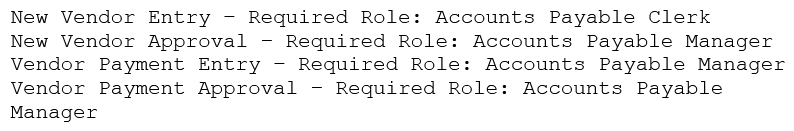
A)
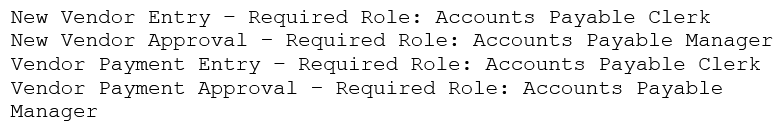
B)
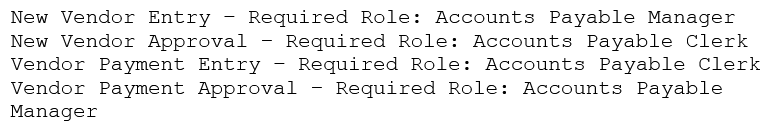
C)
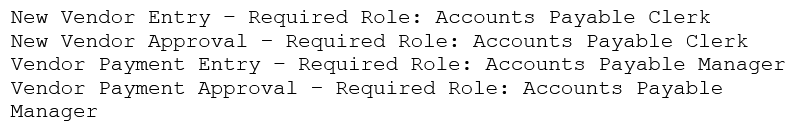
D)

Unlock Deck
Unlock for access to all 1164 flashcards in this deck.
Unlock Deck
k this deck
28
A security consultant discovers that an organization is using the PCL protocol to print documents, utilizing the default driver and print settings. Which of the following is the MOST likely risk in this situation?
A) An attacker can access and change the printer configuration.
B) SNMP data leaving the printer will not be properly encrypted.
C) An MITM attack can reveal sensitive information.
D) An attacker can easily inject malicious code into the printer firmware.
E) Attackers can use the PCL protocol to bypass the firewall of client computers.
A) An attacker can access and change the printer configuration.
B) SNMP data leaving the printer will not be properly encrypted.
C) An MITM attack can reveal sensitive information.
D) An attacker can easily inject malicious code into the printer firmware.
E) Attackers can use the PCL protocol to bypass the firewall of client computers.

Unlock Deck
Unlock for access to all 1164 flashcards in this deck.
Unlock Deck
k this deck
29
Joe, an employee, wants to show his colleagues how much he knows about smartphones. Joe demonstrates a free movie application that he installed from a third party on his corporate smartphone. Joe's colleagues were unable to find the application in the app stores. Which of the following allowed Joe to install the application? (Choose two.)
A) Near-field communication.
B) Rooting/jailbreaking
C) Ad-hoc connections
D) Tethering
E) Sideloading
A) Near-field communication.
B) Rooting/jailbreaking
C) Ad-hoc connections
D) Tethering
E) Sideloading

Unlock Deck
Unlock for access to all 1164 flashcards in this deck.
Unlock Deck
k this deck
30
Which of the following encryption methods does PKI typically use to securely protect keys?
A) Elliptic curve
B) Digital signatures
C) Asymmetric
D) Obfuscation
A) Elliptic curve
B) Digital signatures
C) Asymmetric
D) Obfuscation

Unlock Deck
Unlock for access to all 1164 flashcards in this deck.
Unlock Deck
k this deck
31
An attacker compromises a public CA and issues unauthorized X.509 certificates for Company.com. In the future, Company.com wants to mitigate the impact of similar incidents. Which of the following would assist Company.com with its goal?
A) Certificate pinning
B) Certificate stapling
C) Certificate chaining
D) Certificate with extended validation
A) Certificate pinning
B) Certificate stapling
C) Certificate chaining
D) Certificate with extended validation

Unlock Deck
Unlock for access to all 1164 flashcards in this deck.
Unlock Deck
k this deck
32
A security administrator has found a hash in the environment known to belong to malware. The administrator then finds this file to be in in the preupdate area of the OS, which indicates it was pushed from the central patch system. File: winx86_adobe_flash_upgrade.exe Hash: 99ac28bede43ab869b853ba62c4ea243 The administrator pulls a report from the patch management system with the following output: 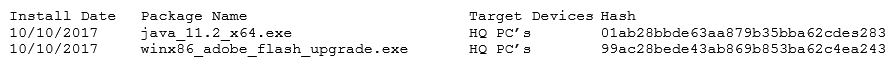 Given the above outputs, which of the following MOST likely happened?
Given the above outputs, which of the following MOST likely happened?
A) The file was corrupted after it left the patch system.
B) The file was infected when the patch manager downloaded it.
C) The file was not approved in the application whitelist system.
D) The file was embedded with a logic bomb to evade detection.
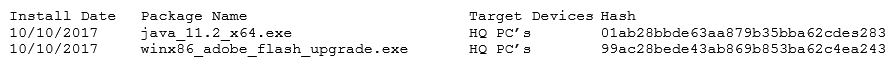 Given the above outputs, which of the following MOST likely happened?
Given the above outputs, which of the following MOST likely happened?A) The file was corrupted after it left the patch system.
B) The file was infected when the patch manager downloaded it.
C) The file was not approved in the application whitelist system.
D) The file was embedded with a logic bomb to evade detection.

Unlock Deck
Unlock for access to all 1164 flashcards in this deck.
Unlock Deck
k this deck
33
Which of the following security controls does an iris scanner provide?
A) Logical
B) Administrative
C) Corrective
D) Physical
E) Detective
F) Deterrent
A) Logical
B) Administrative
C) Corrective
D) Physical
E) Detective
F) Deterrent

Unlock Deck
Unlock for access to all 1164 flashcards in this deck.
Unlock Deck
k this deck
34
A department head at a university resigned on the first day of the spring semester. It was subsequently determined that the department head deleted numerous files and directories from the server-based home directory while the campus was closed. Which of the following policies or procedures could have prevented this from occurring?
A) Time-of-day restrictions
B) Permission auditing and review
C) Offboarding
D) Account expiration
A) Time-of-day restrictions
B) Permission auditing and review
C) Offboarding
D) Account expiration

Unlock Deck
Unlock for access to all 1164 flashcards in this deck.
Unlock Deck
k this deck
35
A database backup schedule consists of weekly full backups performed on Saturday at 12:00 a.m. and daily differential backups also performed at 12:00 a.m. If the database is restored on Tuesday afternoon, which of the following is the number of individual backups that would need to be applied to complete the database recovery?
A) 1
B) 2
C) 3
D) 4
A) 1
B) 2
C) 3
D) 4

Unlock Deck
Unlock for access to all 1164 flashcards in this deck.
Unlock Deck
k this deck
36
Which of the following implements two-factor authentication?
A) A phone system requiring a PIN to make a call
B) At ATM requiring a credit card and PIN
C) A computer requiring username and password
D) A datacenter mantrap requiring fingerprint and iris scan
A) A phone system requiring a PIN to make a call
B) At ATM requiring a credit card and PIN
C) A computer requiring username and password
D) A datacenter mantrap requiring fingerprint and iris scan

Unlock Deck
Unlock for access to all 1164 flashcards in this deck.
Unlock Deck
k this deck
37
Ann, a security administrator, has been instructed to perform fuzz-based testing on the company's applications. Which of the following best describes what she will do?
A) Enter random or invalid data into the application in an attempt to cause it to fault
B) Work with the developers to eliminate horizontal privilege escalation opportunities
C) Test the applications for the existence of built-in- back doors left by the developers
D) Hash the application to verify it won't cause a false positive on the HIPS
A) Enter random or invalid data into the application in an attempt to cause it to fault
B) Work with the developers to eliminate horizontal privilege escalation opportunities
C) Test the applications for the existence of built-in- back doors left by the developers
D) Hash the application to verify it won't cause a false positive on the HIPS

Unlock Deck
Unlock for access to all 1164 flashcards in this deck.
Unlock Deck
k this deck
38
A network administrator at a small office wants to simplify the configuration of mobile clients connecting to an encrypted wireless network. Which of the following should be implemented in the administrator does not want to provide the wireless password or he certificate to the employees?
A) WPS
B) 802.1x
C) WPA2-PSK
D) TKIP
A) WPS
B) 802.1x
C) WPA2-PSK
D) TKIP

Unlock Deck
Unlock for access to all 1164 flashcards in this deck.
Unlock Deck
k this deck
39
When trying to log onto a company's new ticketing system, some employees receive the following message: Access denied: too many concurrent sessions . The ticketing system was recently installed on a small VM with only the recommended hardware specifications. Which of the following is the MOST likely cause for this error message?
A) Network resources have been exceeded.
B) The software is out of licenses.
C) The VM does not have enough processing power.
D) The firewall is misconfigured.
A) Network resources have been exceeded.
B) The software is out of licenses.
C) The VM does not have enough processing power.
D) The firewall is misconfigured.

Unlock Deck
Unlock for access to all 1164 flashcards in this deck.
Unlock Deck
k this deck
40
As part of a new industry regulation, companies are required to utilize secure, standardized OS settings. A technical must ensure the OS settings are hardened. Which of the following is the BEST way to do this?
A) Use a vulnerability scanner.
B) Use a configuration compliance scanner.
C) Use a passive, in-line scanner.
D) Use a protocol analyzer.
A) Use a vulnerability scanner.
B) Use a configuration compliance scanner.
C) Use a passive, in-line scanner.
D) Use a protocol analyzer.

Unlock Deck
Unlock for access to all 1164 flashcards in this deck.
Unlock Deck
k this deck
41
Which of the following network vulnerability scan indicators BEST validates a successful, active scan?
A) The scan job is scheduled to run during off-peak hours.
B) The scan output lists SQL injection attack vectors.
C) The scan data identifies the use of privileged-user credentials.
D) The scan results identify the hostname and IP address.
A) The scan job is scheduled to run during off-peak hours.
B) The scan output lists SQL injection attack vectors.
C) The scan data identifies the use of privileged-user credentials.
D) The scan results identify the hostname and IP address.

Unlock Deck
Unlock for access to all 1164 flashcards in this deck.
Unlock Deck
k this deck
42
A system administrator wants to provide balance between the security of a wireless network and usability. The administrator is concerned with wireless encryption compatibility of older devices used by some employees. Which of the following would provide strong security and backward compatibility when accessing the wireless network?
A) Open wireless network and SSL VPN
B) WPA using a preshared key
C) WPA2 using a RADIUS back-end for 802.1x authentication
D) WEP with a 40-bit key
A) Open wireless network and SSL VPN
B) WPA using a preshared key
C) WPA2 using a RADIUS back-end for 802.1x authentication
D) WEP with a 40-bit key

Unlock Deck
Unlock for access to all 1164 flashcards in this deck.
Unlock Deck
k this deck
43
Which of the following attack types BEST describes a client-side attack that is used to manipulate an HTML iframe with JavaScript code via a web browser?
A) Buffer overflow
B) MITM
C) XSS
D) SQLi
A) Buffer overflow
B) MITM
C) XSS
D) SQLi

Unlock Deck
Unlock for access to all 1164 flashcards in this deck.
Unlock Deck
k this deck
44
A security analyst is hardening an authentication server. One of the primary requirements is to ensure there is mutual authentication and delegation. Given these requirements, which of the following technologies should the analyst recommend and configure?
A) LDAP services
B) Kerberos services
C) NTLM services
D) CHAP services
A) LDAP services
B) Kerberos services
C) NTLM services
D) CHAP services

Unlock Deck
Unlock for access to all 1164 flashcards in this deck.
Unlock Deck
k this deck
45
An analyst is reviewing a simple program for potential security vulnerabilities before being deployed to a Windows server. Given the following code: 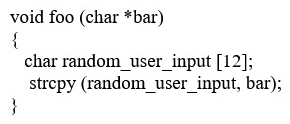 Which of the following vulnerabilities is present?
Which of the following vulnerabilities is present?
A) Bad memory pointer
B) Buffer overflow
C) Integer overflow
D) Backdoor
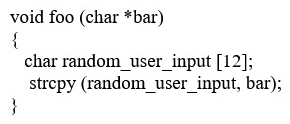 Which of the following vulnerabilities is present?
Which of the following vulnerabilities is present?A) Bad memory pointer
B) Buffer overflow
C) Integer overflow
D) Backdoor

Unlock Deck
Unlock for access to all 1164 flashcards in this deck.
Unlock Deck
k this deck
46
Which of the following would MOST likely appear in an uncredentialed vulnerability scan?
A) Self-signed certificates
B) Missing patches
C) Auditing parameters
D) Inactive local accounts
A) Self-signed certificates
B) Missing patches
C) Auditing parameters
D) Inactive local accounts

Unlock Deck
Unlock for access to all 1164 flashcards in this deck.
Unlock Deck
k this deck
47
Which of the following is the BEST explanation of why control diversity is important in a defense-in-depth architecture?
A) Social engineering is used to bypass technical controls, so having diversity in controls minimizes the risk of demographic exploitation
B) Hackers often impact the effectiveness of more than one control, so having multiple copies of individual controls provides redundancy
C) Technical exploits to defeat controls are released almost every day; control diversity provides overlapping protection.
D) Defense-in-depth relies on control diversity to provide multiple levels of network hierarchy that allow user domain segmentation
A) Social engineering is used to bypass technical controls, so having diversity in controls minimizes the risk of demographic exploitation
B) Hackers often impact the effectiveness of more than one control, so having multiple copies of individual controls provides redundancy
C) Technical exploits to defeat controls are released almost every day; control diversity provides overlapping protection.
D) Defense-in-depth relies on control diversity to provide multiple levels of network hierarchy that allow user domain segmentation

Unlock Deck
Unlock for access to all 1164 flashcards in this deck.
Unlock Deck
k this deck
48
A security analyst observes the following events in the logs of an employee workstation: 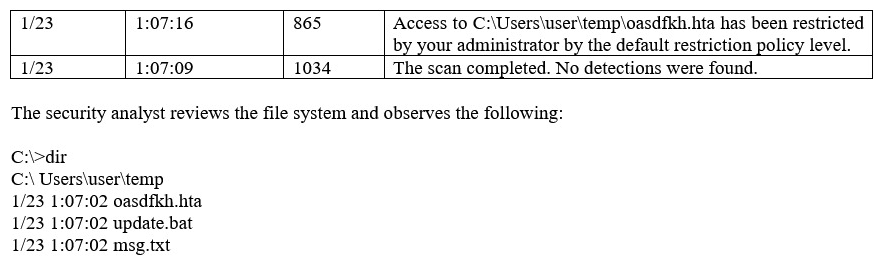 Given the information provided, which of the following MOST likely occurred on the workstation?
Given the information provided, which of the following MOST likely occurred on the workstation?
A) Application whitelisting controls blocked an exploit payload from executing.
B) Antivirus software found and quarantined three malware files.
C) Automatic updates were initiated but failed because they had not been approved.
D) The SIEM log agent was not tuned properly and reported a false positive.
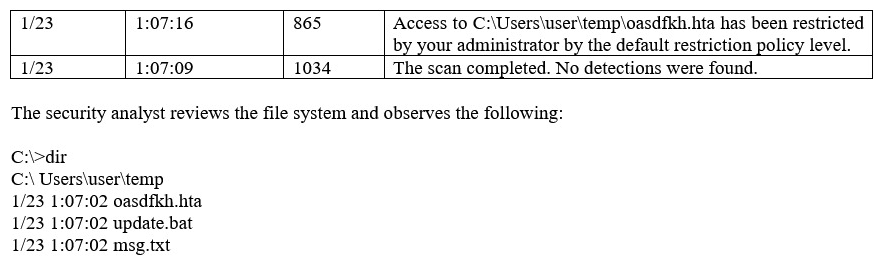 Given the information provided, which of the following MOST likely occurred on the workstation?
Given the information provided, which of the following MOST likely occurred on the workstation?A) Application whitelisting controls blocked an exploit payload from executing.
B) Antivirus software found and quarantined three malware files.
C) Automatic updates were initiated but failed because they had not been approved.
D) The SIEM log agent was not tuned properly and reported a false positive.

Unlock Deck
Unlock for access to all 1164 flashcards in this deck.
Unlock Deck
k this deck
49
Which of the following cryptographic attacks would salting of passwords render ineffective?
A) Brute force
B) Dictionary
C) Rainbow tables
D) Birthday
A) Brute force
B) Dictionary
C) Rainbow tables
D) Birthday

Unlock Deck
Unlock for access to all 1164 flashcards in this deck.
Unlock Deck
k this deck
50
An application team is performing a load-balancing test for a critical application during off-hours and has requested access to the load balancer to review which servers are up without having the administrator on call. The security analyst is hesitant to give the application team full access due to other critical applications running on the load balancer. Which of the following is the BEST solution for security analyst to process the request?
A) Give the application team administrator access during off-hours.
B) Disable other critical applications before granting the team access.
C) Give the application team read-only access.
D) Share the account with the application team.
A) Give the application team administrator access during off-hours.
B) Disable other critical applications before granting the team access.
C) Give the application team read-only access.
D) Share the account with the application team.

Unlock Deck
Unlock for access to all 1164 flashcards in this deck.
Unlock Deck
k this deck
51
An organization wishes to provide better security for its name resolution services. Which of the following technologies BEST supports the deployment of DNSSEC at the organization?
A) LDAP
B) TPM
C) TLS
D) SSL
E) PKI
A) LDAP
B) TPM
C) TLS
D) SSL
E) PKI

Unlock Deck
Unlock for access to all 1164 flashcards in this deck.
Unlock Deck
k this deck
52
A user clicked an email link that led to a website than infected the workstation with a virus. The virus encrypted all the network shares to which the user had access. The virus was not deleted or blocked by the company's email filter, website filter, or antivirus. Which of the following describes what occurred?
A) The user's account was over-privileged.
B) Improper error handling triggered a false negative in all three controls.
C) The email originated from a private email server with no malware protection.
D) The virus was a zero-day attack.
A) The user's account was over-privileged.
B) Improper error handling triggered a false negative in all three controls.
C) The email originated from a private email server with no malware protection.
D) The virus was a zero-day attack.

Unlock Deck
Unlock for access to all 1164 flashcards in this deck.
Unlock Deck
k this deck
53
An administrator is replacing a wireless router. The configuration of the old wireless router was not documented before it stopped functioning. The equipment connecting to the wireless network uses older legacy equipment that was manufactured prior to the release of the 802.11i standard. Which of the following configuration options should the administrator select for the new wireless router?
A) WPA+CCMP
B) WPA2+CCMP
C) WPA+TKIP
D) WPA2+TKIP
A) WPA+CCMP
B) WPA2+CCMP
C) WPA+TKIP
D) WPA2+TKIP

Unlock Deck
Unlock for access to all 1164 flashcards in this deck.
Unlock Deck
k this deck
54
Which of the following occurs when the security of a web application relies on JavaScript for input validation?
A) The integrity of the data is at risk.
B) The security of the application relies on antivirus.
C) A host-based firewall is required.
D) The application is vulnerable to race conditions.
A) The integrity of the data is at risk.
B) The security of the application relies on antivirus.
C) A host-based firewall is required.
D) The application is vulnerable to race conditions.

Unlock Deck
Unlock for access to all 1164 flashcards in this deck.
Unlock Deck
k this deck
55
A system administrator wants to provide for and enforce wireless access accountability during events where external speakers are invited to make presentations to a mixed audience of employees and non-employees. Which of the following should the administrator implement?
A) Shared accounts
B) Preshared passwords
C) Least privilege
D) Sponsored guest
A) Shared accounts
B) Preshared passwords
C) Least privilege
D) Sponsored guest

Unlock Deck
Unlock for access to all 1164 flashcards in this deck.
Unlock Deck
k this deck
56
A company is terminating an employee for misbehavior. Which of the following steps is MOST important in the process of disengagement from this employee?
A) Obtain a list of passwords used by the employee.
B) Generate a report on outstanding projects the employee handled.
C) Have the employee surrender company identification.
D) Have the employee sign an NDA before departing.
A) Obtain a list of passwords used by the employee.
B) Generate a report on outstanding projects the employee handled.
C) Have the employee surrender company identification.
D) Have the employee sign an NDA before departing.

Unlock Deck
Unlock for access to all 1164 flashcards in this deck.
Unlock Deck
k this deck
57
A company is developing a new secure technology and requires computers being used for development to be isolated. Which of the following should be implemented to provide the MOST secure environment?
A) A perimeter firewall and IDS
B) An air gapped computer network
C) A honeypot residing in a DMZ
D) An ad hoc network with NAT
E) A bastion host
A) A perimeter firewall and IDS
B) An air gapped computer network
C) A honeypot residing in a DMZ
D) An ad hoc network with NAT
E) A bastion host

Unlock Deck
Unlock for access to all 1164 flashcards in this deck.
Unlock Deck
k this deck
58
Two users need to send each other emails over unsecured channels. The system should support the principle of non-repudiation. Which of the following should be used to sign the user's certificates?
A) RA
B) CA
C) CRL
D) CSR
A) RA
B) CA
C) CRL
D) CSR

Unlock Deck
Unlock for access to all 1164 flashcards in this deck.
Unlock Deck
k this deck
59
A company hires a consulting firm to crawl its Active Directory network with a non-domain account looking for unpatched systems. Actively taking control of systems is out of scope, as is the creation of new administrator accounts. For which of the following is the company hiring the consulting firm?
A) Vulnerability scanning
B) Penetration testing
C) Application fuzzing
D) User permission auditing
A) Vulnerability scanning
B) Penetration testing
C) Application fuzzing
D) User permission auditing

Unlock Deck
Unlock for access to all 1164 flashcards in this deck.
Unlock Deck
k this deck
60
Ann. An employee in the payroll department, has contacted the help desk citing multiple issues with her device, including: Slow performance Word documents, PDFs, and images no longer opening A pop-up Ann states the issues began after she opened an invoice that a vendor emailed to her. Upon opening the invoice, she had to click several security warnings to view it in her word processor. With which of the following is the device MOST likely infected?
A) Spyware
B) Crypto-malware
C) Rootkit
D) Backdoor
A) Spyware
B) Crypto-malware
C) Rootkit
D) Backdoor

Unlock Deck
Unlock for access to all 1164 flashcards in this deck.
Unlock Deck
k this deck
61
The availability of a system has been labeled as the highest priority. Which of the following should be focused on the MOST to ensure the objective?
A) Authentication
B) HVAC
C) Full-disk encryption
D) File integrity checking
A) Authentication
B) HVAC
C) Full-disk encryption
D) File integrity checking

Unlock Deck
Unlock for access to all 1164 flashcards in this deck.
Unlock Deck
k this deck
62
Which of the following precautions MINIMIZES the risk from network attacks directed at multifunction printers, as well as the impact on functionality at the same time?
A) Isolating the systems using VLANs
B) Installing a software-based IPS on all devices
C) Enabling full disk encryption
D) Implementing a unique user PIN access functions
A) Isolating the systems using VLANs
B) Installing a software-based IPS on all devices
C) Enabling full disk encryption
D) Implementing a unique user PIN access functions

Unlock Deck
Unlock for access to all 1164 flashcards in this deck.
Unlock Deck
k this deck
63
Which of the following would meet the requirements for multifactor authentication?
A) Username, PIN, and employee ID number
B) Fingerprint and password
C) Smart card and hardware token
D) Voice recognition and retina scan
A) Username, PIN, and employee ID number
B) Fingerprint and password
C) Smart card and hardware token
D) Voice recognition and retina scan

Unlock Deck
Unlock for access to all 1164 flashcards in this deck.
Unlock Deck
k this deck
64
A security analyst is performing a quantitative risk analysis. The risk analysis should show the potential monetary loss each time a threat or event occurs. Given this requirement, which of the following concepts would assist the analyst in determining this value? (Choose two.)
A) ALE
B) AV
C) ARO
D) EF
E) ROI
A) ALE
B) AV
C) ARO
D) EF
E) ROI

Unlock Deck
Unlock for access to all 1164 flashcards in this deck.
Unlock Deck
k this deck
65
Which of the following are methods to implement HA in a web application server environment? (Choose two.)
A) Load balancers
B) Application layer firewalls
C) Reverse proxies
D) VPN concentrators
E) Routers
A) Load balancers
B) Application layer firewalls
C) Reverse proxies
D) VPN concentrators
E) Routers

Unlock Deck
Unlock for access to all 1164 flashcards in this deck.
Unlock Deck
k this deck
66
A security analyst is hardening a web server, which should allow a secure certificate-based session using the organization's PKI infrastructure. The web server should also utilize the latest security techniques and standards. Given this set of requirements, which of the following techniques should the analyst implement to BEST meet these requirements? (Choose two.)
A) Install an X- 509-compliant certificate.
B) Implement a CRL using an authorized CA.
C) Enable and configure TLS on the server.
D) Install a certificate signed by a public CA.
E) Configure the web server to use a host header.
A) Install an X- 509-compliant certificate.
B) Implement a CRL using an authorized CA.
C) Enable and configure TLS on the server.
D) Install a certificate signed by a public CA.
E) Configure the web server to use a host header.

Unlock Deck
Unlock for access to all 1164 flashcards in this deck.
Unlock Deck
k this deck
67
A new firewall has been places into service at an organization. However, a configuration has not been entered on the firewall. Employees on the network segment covered by the new firewall report they are unable to access the network. Which of the following steps should be completed to BEST resolve the issue?
A) The firewall should be configured to prevent user traffic form matching the implicit deny rule.
B) The firewall should be configured with access lists to allow inbound and outbound traffic.
C) The firewall should be configured with port security to allow traffic.
D) The firewall should be configured to include an explicit deny rule.
A) The firewall should be configured to prevent user traffic form matching the implicit deny rule.
B) The firewall should be configured with access lists to allow inbound and outbound traffic.
C) The firewall should be configured with port security to allow traffic.
D) The firewall should be configured to include an explicit deny rule.

Unlock Deck
Unlock for access to all 1164 flashcards in this deck.
Unlock Deck
k this deck
68
Joe, a security administrator, needs to extend the organization's remote access functionality to be used by staff while travelling. Joe needs to maintain separate access control functionalities for internal, external, and VOIP services. Which of the following represents the BEST access technology for Joe to use?
A) RADIUS
B) TACACS+
C) Diameter
D) Kerberos
A) RADIUS
B) TACACS+
C) Diameter
D) Kerberos

Unlock Deck
Unlock for access to all 1164 flashcards in this deck.
Unlock Deck
k this deck
69
A dumpster diver recovers several hard drives from a company and is able to obtain confidential data from one of the hard drives. The company then discovers its information is posted online. Which of the following methods would have MOST likely prevented the data from being exposed?
A) Removing the hard drive from its enclosure
B) Using software to repeatedly rewrite over the disk space
C) Using Blowfish encryption on the hard drives
D) Using magnetic fields to erase the data
A) Removing the hard drive from its enclosure
B) Using software to repeatedly rewrite over the disk space
C) Using Blowfish encryption on the hard drives
D) Using magnetic fields to erase the data

Unlock Deck
Unlock for access to all 1164 flashcards in this deck.
Unlock Deck
k this deck
70
A systems administrator is reviewing the following information from a compromised server: 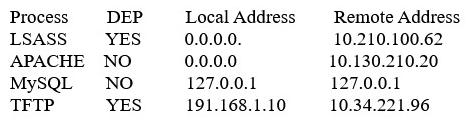 Given the above information, which of the following processes was MOST likely exploited via a remote buffer overflow attack?
Given the above information, which of the following processes was MOST likely exploited via a remote buffer overflow attack?
A) Apache
B) LSASS
C) MySQL
D) TFTP
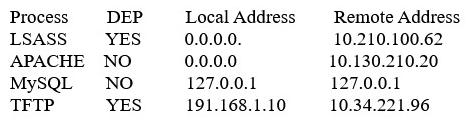 Given the above information, which of the following processes was MOST likely exploited via a remote buffer overflow attack?
Given the above information, which of the following processes was MOST likely exploited via a remote buffer overflow attack?A) Apache
B) LSASS
C) MySQL
D) TFTP

Unlock Deck
Unlock for access to all 1164 flashcards in this deck.
Unlock Deck
k this deck
71
Which of the following cryptography algorithms will produce a fixed-length, irreversible output?
A) AES
B) 3DES
C) RSA
D) MD5
A) AES
B) 3DES
C) RSA
D) MD5

Unlock Deck
Unlock for access to all 1164 flashcards in this deck.
Unlock Deck
k this deck
72
An application developer is designing an application involving secure transports from one service to another that will pass over port 80 for a request. Which of the following secure protocols is the developer MOST likely to use?
A) FTPS
B) SFTP
C) SSL
D) LDAPS
E) SSH
A) FTPS
B) SFTP
C) SSL
D) LDAPS
E) SSH

Unlock Deck
Unlock for access to all 1164 flashcards in this deck.
Unlock Deck
k this deck
73
After an identified security breach, an analyst is tasked to initiate the IR process. Which of the following is the NEXT step the analyst should take?
A) Recovery
B) Identification
C) Preparation
D) Documentation
E) Escalation
A) Recovery
B) Identification
C) Preparation
D) Documentation
E) Escalation

Unlock Deck
Unlock for access to all 1164 flashcards in this deck.
Unlock Deck
k this deck
74
A security analyst is testing both Windows and Linux systems for unauthorized DNS zone transfers within a LAN on comptia.org from example.org. Which of the following commands should the security analyst use? (Choose two.)
A)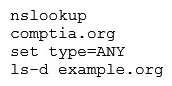
B)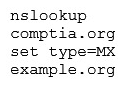
C) dig -axfr comptia.org @example.org
D) ipconfig /flushDNS
E)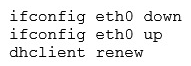
A)
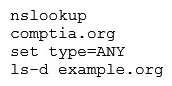
B)
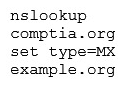
C) dig -axfr comptia.org @example.org
D) ipconfig /flushDNS
E)

Unlock Deck
Unlock for access to all 1164 flashcards in this deck.
Unlock Deck
k this deck
75
An organization's file server has been virtualized to reduce costs. Which of the following types of backups would be MOST appropriate for the particular file server?
A) Snapshot
B) Full
C) Incremental
D) Differential
A) Snapshot
B) Full
C) Incremental
D) Differential

Unlock Deck
Unlock for access to all 1164 flashcards in this deck.
Unlock Deck
k this deck
76
Before an infection was detected, several of the infected devices attempted to access a URL that was similar to the company name but with two letters transposed. Which of the following BEST describes the attack vector used to infect the devices?
A) Cross-site scripting
B) DNS poisoning
C) Typo squatting
D) URL hijacking
A) Cross-site scripting
B) DNS poisoning
C) Typo squatting
D) URL hijacking

Unlock Deck
Unlock for access to all 1164 flashcards in this deck.
Unlock Deck
k this deck
77
Which of the following are the MAIN reasons why a systems administrator would install security patches in a staging environment before the patches are applied to the production server? (Choose two.)
A) To prevent server availability issues
B) To verify the appropriate patch is being installed
C) To generate a new baseline hash after patching
D) To allow users to test functionality
E) To ensure users are trained on new functionality
A) To prevent server availability issues
B) To verify the appropriate patch is being installed
C) To generate a new baseline hash after patching
D) To allow users to test functionality
E) To ensure users are trained on new functionality

Unlock Deck
Unlock for access to all 1164 flashcards in this deck.
Unlock Deck
k this deck
78
A systems administrator wants to protect data stored on mobile devices that are used to scan and record assets in a warehouse. The control must automatically destroy the secure container of mobile devices if they leave the warehouse. Which of the following should the administrator implement? (Choose two.)
A) Geofencing
B) Remote wipe
C) Near-field communication
D) Push notification services
E) Containerization
A) Geofencing
B) Remote wipe
C) Near-field communication
D) Push notification services
E) Containerization

Unlock Deck
Unlock for access to all 1164 flashcards in this deck.
Unlock Deck
k this deck
79
A vulnerability scanner that uses its running service's access level to better assess vulnerabilities across multiple assets within an organization is performing a:
A) Credentialed scan.
B) Non-intrusive scan.
C) Privilege escalation test.
D) Passive scan.
A) Credentialed scan.
B) Non-intrusive scan.
C) Privilege escalation test.
D) Passive scan.

Unlock Deck
Unlock for access to all 1164 flashcards in this deck.
Unlock Deck
k this deck
80
A manager wants to distribute a report to several other managers within the company. Some of them reside in remote locations that are not connected to the domain but have a local server. Because there is sensitive data within the report and the size of the report is beyond the limit of the email attachment size, emailing the report is not an option. Which of the following protocols should be implemented to distribute the report securely? (Choose three.)
A) S/MIME
B) SSH
C) SNMPv3
D) FTPS
E) SRTP
F) HTTPS
G) LDAPS
A) S/MIME
B) SSH
C) SNMPv3
D) FTPS
E) SRTP
F) HTTPS
G) LDAPS

Unlock Deck
Unlock for access to all 1164 flashcards in this deck.
Unlock Deck
k this deck


