Exam 4: EC-Council Certified CISO
Question
Question
Question
Question
Question
Question
Question
Question
Question
Question
Question
Question
Question
Question
Question
Question
Question
Question
Question
Question
Question
Question
Question
Question
Question
Question
Question

Unlock Deck
Sign up to unlock the cards in this deck!
Unlock Deck
Unlock Deck
1/27
Play
Full screen (f)
Exam 4: EC-Council Certified CISO
1
Heather, a computer forensics investigator, is assisting a group of investigators working on a large computer fraud case involving over 20 people. These 20 people, working in different offices, allegedly siphoned off money from many different client accounts. Heather responsibility is to find out how the accused people communicated between each other. She has searched their email and their computers and has not found any useful evidence. Heather then finds some possibly useful evidence under the desk of one of the accused. In an envelope she finds a piece of plastic with numerous holes cut out of it. Heather then finds the same exact piece of plastic with holes at many of the other accused peoples desks. Heather believes that the 20 people involved in the case were using a cipher to send secret messages in between each other. What type of cipher was used by the accused in this case?
A) Grill cipher
B) Null cipher
C) Text semagram
D) Visual semagram
A) Grill cipher
B) Null cipher
C) Text semagram
D) Visual semagram
A
2
Paul is a computer forensics investigator working for Tyler & Company Consultants. Paul has been called upon to help investigate a computer hacking ring broken up by the local police. Paul begins to inventory the PCs found in the hackers hideout. Paul then comes across a PDA left by them that is attached to a number of different peripheral devices. What is the first step that Paul must take with the PDA to ensure the integrity of the investigation?
A) Place PDA, including all devices, in an antistatic bag
B) Unplug all connected devices
C) Power off all devices if currently on
D) Photograph and document the peripheral devices
A) Place PDA, including all devices, in an antistatic bag
B) Unplug all connected devices
C) Power off all devices if currently on
D) Photograph and document the peripheral devices
D
3
A forensics investigator is searching the hard drive of a computer for files that were recently moved to the Recycle Bin. He searches for files in C:\RECYCLED using a command line tool but does not find anything. What is the reason for this?
A) He should search in C:\Windows\System32\RECYCLED folder
B) The Recycle Bin does not exist on the hard drive
C) The files are hidden and he must use switch to view them
D) Only FAT system contains RECYCLED folder and not NTFS
A) He should search in C:\Windows\System32\RECYCLED folder
B) The Recycle Bin does not exist on the hard drive
C) The files are hidden and he must use switch to view them
D) Only FAT system contains RECYCLED folder and not NTFS
C
4
What must an investigator do before disconnecting an iPod from any type of computer?
A) Unmount the iPod
B) Mount the iPod
C) Disjoin the iPod
D) Join the iPod
A) Unmount the iPod
B) Mount the iPod
C) Disjoin the iPod
D) Join the iPod

Unlock Deck
Unlock for access to all 27 flashcards in this deck.
Unlock Deck
k this deck
5
What is the slave device connected to the secondary IDE controller on a Linux OS referred to?
A) hda
B) hdd
C) hdb
D) hdc
A) hda
B) hdd
C) hdb
D) hdc

Unlock Deck
Unlock for access to all 27 flashcards in this deck.
Unlock Deck
k this deck
6
An investigator is searching through the firewall logs of a company and notices ICMP packets that are larger than 65,536 bytes. What type of activity is the investigator seeing?
A) Smurf
B) Ping of death
C) Fraggle
D) Nmap scan
A) Smurf
B) Ping of death
C) Fraggle
D) Nmap scan

Unlock Deck
Unlock for access to all 27 flashcards in this deck.
Unlock Deck
k this deck
7
What advantage does the tool Evidor have over the built-in Windows search?
A) It can find deleted files even after they have been physically removed
B) It can find bad sectors on the hard drive
C) It can search slack space
D) It can find files hidden within ADS
A) It can find deleted files even after they have been physically removed
B) It can find bad sectors on the hard drive
C) It can search slack space
D) It can find files hidden within ADS

Unlock Deck
Unlock for access to all 27 flashcards in this deck.
Unlock Deck
k this deck
8
The objective of this act was to protect consumers' personal financial information held by financial institutions and their service providers.
A) Gramm-Leach-Bliley Act
B) Sarbanes-Oxley 2002
C) California SB 1386
D) HIPAA
A) Gramm-Leach-Bliley Act
B) Sarbanes-Oxley 2002
C) California SB 1386
D) HIPAA

Unlock Deck
Unlock for access to all 27 flashcards in this deck.
Unlock Deck
k this deck
9
Under confession, an accused criminal admitted to encrypting child pornography pictures and then hiding them within other pictures. What technique did the accused criminal employ?
A) Typography
B) Steganalysis
C) Picture encoding
D) Steganography
A) Typography
B) Steganalysis
C) Picture encoding
D) Steganography

Unlock Deck
Unlock for access to all 27 flashcards in this deck.
Unlock Deck
k this deck
10
John is working on his company policies and guidelines. The section he is currently working on covers company documents; how they should be handled, stored, and eventually destroyed. John is concerned about the process whereby outdated documents are destroyed. What type of shredder should John write in the guidelines to be used when destroying documents?
A) Strip-cut shredder
B) Cross-cut shredder
C) Cross-hatch shredder
D) Cris-cross shredder
A) Strip-cut shredder
B) Cross-cut shredder
C) Cross-hatch shredder
D) Cris-cross shredder

Unlock Deck
Unlock for access to all 27 flashcards in this deck.
Unlock Deck
k this deck
11
What hashing method is used to password protect Blackberry devices?
A) AES
B) RC5
C) MD5
D) SHA-1
A) AES
B) RC5
C) MD5
D) SHA-1

Unlock Deck
Unlock for access to all 27 flashcards in this deck.
Unlock Deck
k this deck
12
What technique used by Encase makes it virtually impossible to tamper with evidence once it has been acquired?
A) Every byte of the file(s) is given an MD5 hash to match against a master file
B) Every byte of the file(s) is verified using 32-bit CRC
C) Every byte of the file(s) is copied to three different hard drives
D) Every byte of the file(s) is encrypted using three different methods
A) Every byte of the file(s) is given an MD5 hash to match against a master file
B) Every byte of the file(s) is verified using 32-bit CRC
C) Every byte of the file(s) is copied to three different hard drives
D) Every byte of the file(s) is encrypted using three different methods

Unlock Deck
Unlock for access to all 27 flashcards in this deck.
Unlock Deck
k this deck
13
Jonathan is a network administrator who is currently testing the internal security of his network. He is attempting to hijack a session, using Ettercap, of a user connected to his Web server. Why will Jonathan not succeed?
A) Only an HTTPS session can be hijacked
B) HTTP protocol does not maintain session
C) Only FTP traffic can be hijacked
D) Only DNS traffic can be hijacked
A) Only an HTTPS session can be hijacked
B) HTTP protocol does not maintain session
C) Only FTP traffic can be hijacked
D) Only DNS traffic can be hijacked

Unlock Deck
Unlock for access to all 27 flashcards in this deck.
Unlock Deck
k this deck
14
A packet is sent to a router that does not have the packet destination address in its route table. How will the packet get to its proper destination?
A) Root Internet servers
B) Border Gateway Protocol
C) Gateway of last resort
D) Reverse DNS
A) Root Internet servers
B) Border Gateway Protocol
C) Gateway of last resort
D) Reverse DNS

Unlock Deck
Unlock for access to all 27 flashcards in this deck.
Unlock Deck
k this deck
15
What layer of the OSI model do TCP and UDP utilize?
A) Data Link
B) Network
C) Transport
D) Session
A) Data Link
B) Network
C) Transport
D) Session

Unlock Deck
Unlock for access to all 27 flashcards in this deck.
Unlock Deck
k this deck
16
When using an iPod and the host computer is running Windows, what file system will be used?
A) iPod+
B) HFS
C) FAT16
D) FAT32
A) iPod+
B) HFS
C) FAT16
D) FAT32

Unlock Deck
Unlock for access to all 27 flashcards in this deck.
Unlock Deck
k this deck
17
What is one method of bypassing a system BIOS password?
A) Removing the processor
B) Removing the CMOS battery
C) Remove all the system memory
D) Login to Windows and disable the BIOS password
A) Removing the processor
B) Removing the CMOS battery
C) Remove all the system memory
D) Login to Windows and disable the BIOS password

Unlock Deck
Unlock for access to all 27 flashcards in this deck.
Unlock Deck
k this deck
18
Where does Encase search to recover NTFS files and folders?
A) MBR
B) MFT
C) Slack space
D) HAL
A) MBR
B) MFT
C) Slack space
D) HAL

Unlock Deck
Unlock for access to all 27 flashcards in this deck.
Unlock Deck
k this deck
19
If you are concerned about a high level of compression but not concerned about any possible data loss, what type of compression would you use?
A) Lossful compression
B) Lossy compression
C) Lossless compression
D) Time-loss compression
A) Lossful compression
B) Lossy compression
C) Lossless compression
D) Time-loss compression

Unlock Deck
Unlock for access to all 27 flashcards in this deck.
Unlock Deck
k this deck
20
Harold is a web designer who has completed a website for ghttech.net. As part of the maintenance agreement he signed with the client, Harold is performing research online and seeing how much exposure the site has received so far. Harold navigates to google.com and types in the following search. link:www.ghttech.net What will this search produce?
A) All sites that ghttech.net links to
B) All sites that link to ghttech.net
C) All search engines that link to .net domains
D) Sites that contain the code: link:www.ghttech.net
A) All sites that ghttech.net links to
B) All sites that link to ghttech.net
C) All search engines that link to .net domains
D) Sites that contain the code: link:www.ghttech.net

Unlock Deck
Unlock for access to all 27 flashcards in this deck.
Unlock Deck
k this deck
21
When searching through file headers for picture file formats, what should be searched to find a JPEG file in hexadecimal format?
A) FF D8 FF E0 00 10
B) FF FF FF FF FF FF
C) FF 00 FF 00 FF 00
D) EF 00 EF 00 EF 00
A) FF D8 FF E0 00 10
B) FF FF FF FF FF FF
C) FF 00 FF 00 FF 00
D) EF 00 EF 00 EF 00

Unlock Deck
Unlock for access to all 27 flashcards in this deck.
Unlock Deck
k this deck
22
To check for POP3 traffic using Ethereal, what port should an investigator search by?
A) 143
B) 25
C) 110
D) 125
A) 143
B) 25
C) 110
D) 125

Unlock Deck
Unlock for access to all 27 flashcards in this deck.
Unlock Deck
k this deck
23
Where are files temporarily written in Unix when printing?
A) /usr/spool
B) /var/print
C) /spool
D) /var/spool
A) /usr/spool
B) /var/print
C) /spool
D) /var/spool

Unlock Deck
Unlock for access to all 27 flashcards in this deck.
Unlock Deck
k this deck
24
Julie is a college student majoring in Information Systems and Computer Science. She is currently writing an essay for her computer crimes class. Julie paper focuses on white-collar crimes in America and how forensics investigators investigate the cases. Julie would like to focus the subject. Julie would like to focus the subject of the essay on the most common type of crime found in corporate America. What crime should Julie focus on?
A) Physical theft
B) Copyright infringement
C) Industrial espionage
D) Denial of Service attacks
A) Physical theft
B) Copyright infringement
C) Industrial espionage
D) Denial of Service attacks

Unlock Deck
Unlock for access to all 27 flashcards in this deck.
Unlock Deck
k this deck
25
Sniffers that place NICs in promiscuous mode work at what layer of the OSI model?
A) Network
B) Transport
C) Physical
D) Data Link
A) Network
B) Transport
C) Physical
D) Data Link

Unlock Deck
Unlock for access to all 27 flashcards in this deck.
Unlock Deck
k this deck
26
Jack Smith is a forensics investigator who works for Mason Computer Investigation Services. He is investigating a computer that was infected by Ramen Virus. 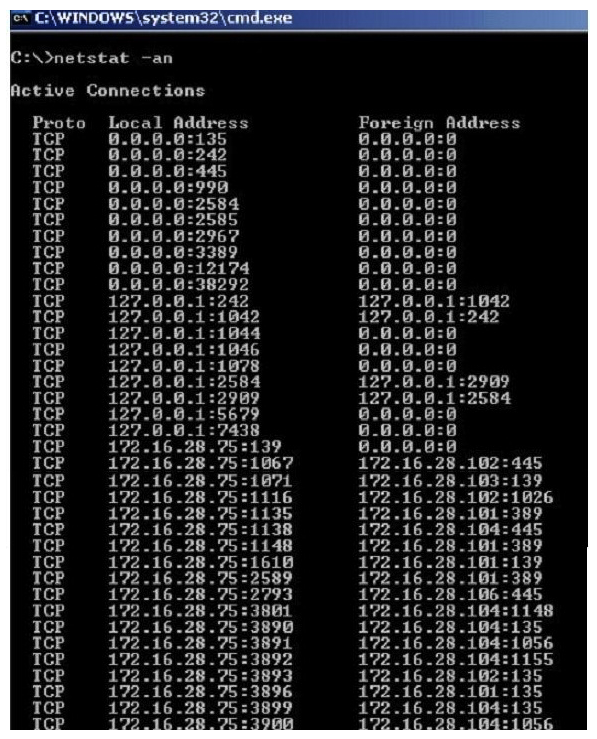 He runs the netstat command on the machine to see its current connections. In the following screenshot, what do the 0.0.0.0 IP addresses signify?
He runs the netstat command on the machine to see its current connections. In the following screenshot, what do the 0.0.0.0 IP addresses signify?
A) Those connections are established
B) Those connections are in listening mode
C) Those connections are in closed/waiting mode
D) Those connections are in timed out/waiting mode
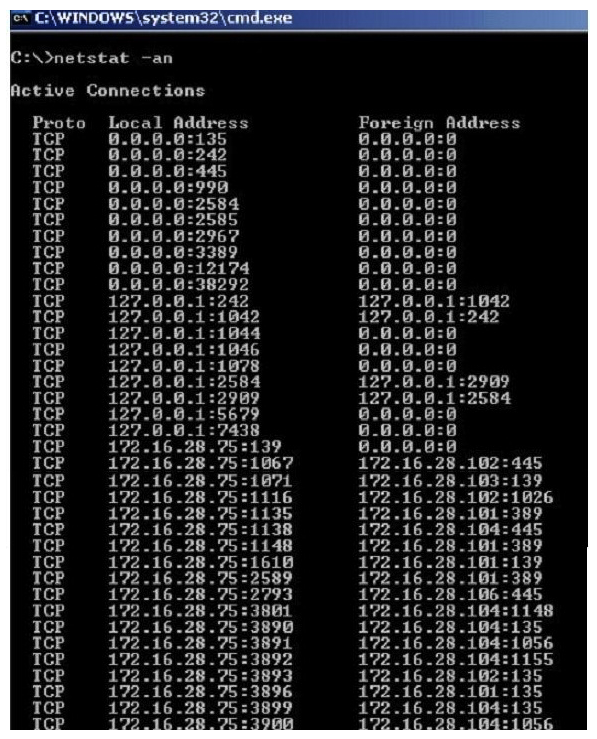 He runs the netstat command on the machine to see its current connections. In the following screenshot, what do the 0.0.0.0 IP addresses signify?
He runs the netstat command on the machine to see its current connections. In the following screenshot, what do the 0.0.0.0 IP addresses signify? A) Those connections are established
B) Those connections are in listening mode
C) Those connections are in closed/waiting mode
D) Those connections are in timed out/waiting mode

Unlock Deck
Unlock for access to all 27 flashcards in this deck.
Unlock Deck
k this deck
27
You have been called in to help with an investigation of an alleged network intrusion. After questioning the members of the company IT department, you search through the server log files to find any trace of the intrusion. After that you decide to telnet into one of the company routers to see if there is any evidence to be found. While connected to the router, you see some unusual activity and believe that the attackers are currently connected to that router. You start up an ethereal session to begin capturing traffic on the router that could be used in the investigation. At what layer of the OSI model are you monitoring while watching traffic to and from the router?
A) Network
B) Transport
C) Data Link
D) Session
A) Network
B) Transport
C) Data Link
D) Session

Unlock Deck
Unlock for access to all 27 flashcards in this deck.
Unlock Deck
k this deck


