Multiple Choice
Given the Nmap request below: 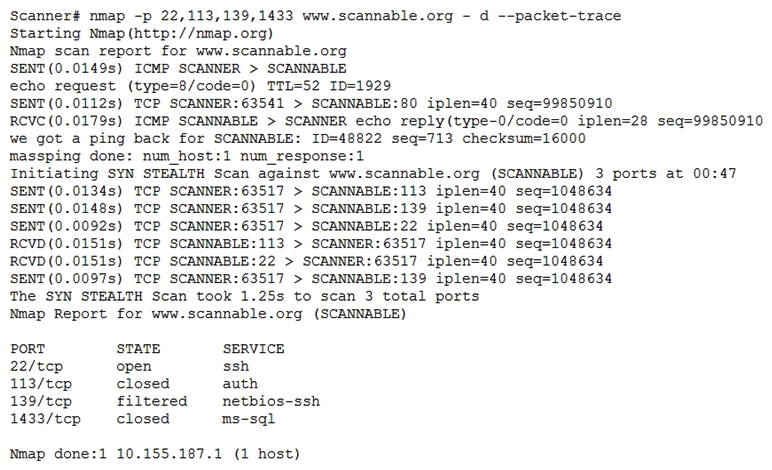 Which of the following actions will an attacker be able to initiate directly against this host?
Which of the following actions will an attacker be able to initiate directly against this host?
A) Password sniffing
B) ARP spoofing
C) A brute-force attack
D) An SQL injection
Correct Answer:

Verified
Correct Answer:
Verified
Related Questions
Q133: The security team at a large corporation
Q134: Which of the following are components of
Q135: When attempting to do a stealth scan
Q136: A cybersecurity analyst is contributing to a
Q137: While planning segmentation for an ICS environment,
Q139: A security analyst gathered forensics from a
Q140: An audit has revealed an organization is
Q141: A team of security analysts has been
Q142: A Chief Security Officer (CSO) is working
Q143: A security analyst received an alert from