Exam 41: Implementing Cisco Collaboration Core Technologies (CLCOR)
Exam 1: Supporting Cisco Data Center System Devices (DCTECH)128 Questions
Exam 2: Cisco Certified Technician Routing & Switching (RSTECH)48 Questions
Exam 3: Understanding Cisco Cybersecurity Operations Fundamentals (CBROPS)141 Questions
Exam 4: Cisco Certified Network Associate (CCNA)411 Questions
Exam 5: Managing Industrial Networks with Cisco Networking Technologies (IMINS)36 Questions
Exam 6: DevNet Associate (DEVASC)134 Questions
Exam 7: Conducting Forensic Analysis and Incident Response Using Cisco CyberOps Technologies (CBRFIR)25 Questions
Exam 8: Implementing Cisco Enterprise Advanced Routing and Services (ENARSI)114 Questions
Exam 9: Implementing Cisco SD-WAN Solutions (ENSDWI)147 Questions
Exam 10: Designing Cisco Enterprise Networks (ENSLD)109 Questions
Exam 11: Designing Cisco Enterprise Wireless Networks (300-425 ENWLSD)106 Questions
Exam 12: Implementing Cisco Enterprise Wireless Networks (300-430 ENWLSI)101 Questions
Exam 13: Automating Cisco Enterprise Solutions (ENAUTO)84 Questions
Exam 14: Implementing Cisco Service Provider Advanced Routing Solutions (SPRI)74 Questions
Exam 15: Implementing Cisco Service Provider VPN Services (SPVI)49 Questions
Exam 16: Designing Cisco Data Center Infrastructure (DCID)73 Questions
Exam 17: Troubleshooting Cisco Data Center Infrastructure (DCIT)84 Questions
Exam 18: Implementing Cisco Application Centric Infrastructure (DCACI)101 Questions
Exam 19: Configuring Cisco MDS 9000 Series Switches (DCSAN)65 Questions
Exam 20: Implementing Cisco Application Centric Infrastructure - Advanced36 Questions
Exam 21: Automating Cisco Data Center Solutions (DCAUTO)36 Questions
Exam 22: Securing Networks with Cisco Firepower (300-710 SNCF)65 Questions
Exam 23: Implementing and Configuring Cisco Identity Services Engine (300-715 SISE)130 Questions
Exam 24: Securing Email with Cisco Email Security Appliance (300-720 SESA)65 Questions
Exam 25: Securing the Web with Cisco Web Security Appliance (300-725 SWSA)75 Questions
Exam 26: Implementing Secure Solutions with Virtual Private Networks (SVPN 300-730)49 Questions
Exam 27: Automating Cisco Security Solutions (SAUTO)75 Questions
Exam 28: Implementing Cisco Collaboration Applications (CLICA)39 Questions
Exam 29: Implementing Cisco Advanced Call Control and Mobility Services (CLASSM)86 Questions
Exam 30: Implementing Cisco Collaboration Cloud and Edge Solutions90 Questions
Exam 31: Implementing Cisco Collaboration Conferencing65 Questions
Exam 32: Automating Cisco Collaboration Solutions (CLAUTO)27 Questions
Exam 33: Implementing DevOps Solutions and Practices using Cisco Platforms (DEVOPS)66 Questions
Exam 34: Developing Solutions Using Cisco IoT and Edge Platforms (DEVIOT)33 Questions
Exam 35: Developing Applications for Cisco Webex and Webex Devices (DEVWBX)41 Questions
Exam 36: Performing CyberOps Using Core Security Technologies (CBRCOR)37 Questions
Exam 37: Implementing Cisco Enterprise Network Core Technologies (ENCOR)106 Questions
Exam 38: Implementing and Operating Cisco Service Provider Network Core Technologies (SPCOR)260 Questions
Exam 39: Implementing and Operating Cisco Data Center Core Technologies (DCCOR)116 Questions
Exam 40: Implementing and Operating Cisco Security Core Technologies208 Questions
Exam 41: Implementing Cisco Collaboration Core Technologies (CLCOR)213 Questions
Exam 42: Developing Applications using Cisco Core Platforms and APIs (DEVCOR)131 Questions
Exam 43: CCDE Design Written145 Questions
Exam 44: Deploying Cisco Unified Contact Center Express660 Questions
Exam 45: Cisco Meraki Solutions Specialist101 Questions
Exam 46: Securing Cisco Networks with Sourcefire FireAMP Endpoints24 Questions
Exam 47: Designing Cisco Unified Contact Center Enterprise (UCCED)227 Questions
Exam 48: Implementing and Supporting Cisco Unified Contact Center Enterprise (UCCEIS)55 Questions
Exam 49: Cisco Collaboration SaaS Authorization Exam47 Questions
Exam 50: Cisco Security Architecture for System Engineers56 Questions
Exam 51: Adopting The Cisco Business Architecture Approach (DTBAA)239 Questions
Exam 52: Cisco Customer Success Manager (CSM)44 Questions
Exam 53: Mastering The Cisco Business Architecture Discipline (DTBAD)36 Questions
Select questions type
An organization is trying to improve their Defense in Depth by blocking malicious destinations prior to a connection being established. The solution must be able to block certain applications from being used within the network. Which product should be used to accomplish this goal?
(Multiple Choice)
4.8/5  (38)
(38)
Which two characteristics of messenger protocols make data exfiltration difficult to detect and prevent? (Choose two.)
(Multiple Choice)
4.7/5  (40)
(40)
In which two ways does Easy Connect help control network access when used with Cisco TrustSec? (Choose two.)
(Multiple Choice)
4.8/5  (30)
(30)
When wired 802.1X authentication is implemented, which two components are required? (Choose two.)
(Multiple Choice)
4.7/5  (35)
(35)
Which two behavioral patterns characterize a ping of death attack? (Choose two.)
(Multiple Choice)
4.9/5  (31)
(31)
Which term describes when the Cisco Firepower downloads threat intelligence updates from Cisco Talos?
(Multiple Choice)
4.9/5  (37)
(37)
Which technology must be used to implement secure VPN connectivity among company branches over a private IP cloud with any-to-any scalable connectivity?
(Multiple Choice)
4.8/5  (37)
(37)
Which network monitoring solution uses streams and pushes operational data to provide a near real-time view of activity?
(Multiple Choice)
4.9/5  (39)
(39)
Which two kinds of attacks are prevented by multifactor authentication? (Choose two.)
(Multiple Choice)
4.8/5  (40)
(40)
Which two conditions are prerequisites for stateful failover for IPsec? (Choose two.)
(Multiple Choice)
4.9/5  (40)
(40)
What is a characteristic of a bridge group in ASA Firewall transparent mode?
(Multiple Choice)
4.8/5  (42)
(42)
What are two list types within Cisco AMP for Endpoints Outbreak Control? (Choose two.)
(Multiple Choice)
4.9/5  (30)
(30)
Which Talos reputation center allows you to track the reputation of IP addresses for email and web traffic?
(Multiple Choice)
4.9/5  (31)
(31)
In which form of attack is alternate encoding, such as hexadecimal representation, most often observed?
(Multiple Choice)
4.8/5  (29)
(29)
Which Cisco product provides proactive endpoint protection and allows administrators to centrally manage the deployment?
(Multiple Choice)
4.9/5  (46)
(46)
When web policies are configured in Cisco Umbrella, what provides the ability to ensure that domains are blocked when they host malware, command and control, phishing, and more threats?
(Multiple Choice)
4.9/5  (36)
(36)
Which proxy mode must be used on Cisco WSA to redirect TCP traffic with WCCP?
(Multiple Choice)
4.8/5  (38)
(38)
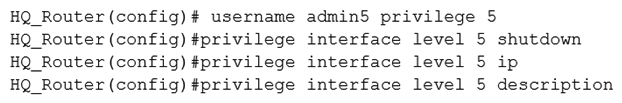 Refer to the exhibit. A network administrator configures command authorization for the admin5 user. What is the admin5 user able to do on HQ_Router after this configuration?
Refer to the exhibit. A network administrator configures command authorization for the admin5 user. What is the admin5 user able to do on HQ_Router after this configuration?
(Multiple Choice)
4.8/5  (35)
(35)
Which two request methods of REST API are valid on the Cisco ASA Platform? (Choose two.)
(Multiple Choice)
4.7/5  (36)
(36)
Which two tasks allow NetFlow on a Cisco ASA 5500 Series firewall? (Choose two.)
(Multiple Choice)
4.9/5  (32)
(32)
Showing 121 - 140 of 213
Filters
- Essay(0)
- Multiple Choice(0)
- Short Answer(0)
- True False(0)
- Matching(0)