Exam 3: CompTIA Advanced Security Practitioner (CASP+) CAS-003
Exam 1: CompTIA A+ Certification Exam: Core 1471 Questions
Exam 2: CompTIA A+ Certification Exam: Core 2409 Questions
Exam 3: CompTIA Advanced Security Practitioner (CASP+) CAS-003442 Questions
Exam 4: CompTIA Advanced Security Practitioner (CASP+) CAS-004107 Questions
Exam 5: CompTIA Cloud Essentials+165 Questions
Exam 6: CompTIA CySA+ Certification Exam (CS0-002)294 Questions
Exam 7: CompTIA Cloud+ (CV0-002)48 Questions
Exam 8: CompTIA Cloud+67 Questions
Exam 9: CompTIA IT Fundamentals387 Questions
Exam 10: CompTIA Network+829 Questions
Exam 11: CompTIA Project+540 Questions
Exam 12: CompTIA PenTest+ Certification Exam165 Questions
Exam 13: CompTIA Server+66 Questions
Exam 14: CompTIA Server+ Certification Exam779 Questions
Exam 15: CompTIA Security+1 k+ Questions
Exam 16: CompTIA Security+ 2021129 Questions
Exam 17: CompTIA CTT+ Essentials378 Questions
Exam 18: CompTIA Linux+252 Questions
Select questions type
A forensics analyst suspects that a breach has occurred. Security logs show the company's OS patch system may be compromised, and it is serving patches that contain a zero-day exploit and backdoor. The analyst extracts an executable file from a packet capture of communication between a client computer and the patch server. Which of the following should the analyst use to confirm this suspicion?
(Multiple Choice)
4.8/5  (25)
(25)
A company has hired an external security consultant to conduct a thorough review of all aspects of corporate security. The company is particularly concerned about unauthorized access to its physical offices resulting in network compromises. Which of the following should the consultant recommend be performed to evaluate potential risks?
(Multiple Choice)
4.8/5  (32)
(32)
With which of the following departments should an engineer for a consulting firm coordinate when determining the control and reporting requirements for storage of sensitive, proprietary customer information?
(Multiple Choice)
4.7/5  (44)
(44)
A security analyst receives an email from a peer that includes a sample of code from a piece of malware found in an application running in the organization's staging environment. During the incident response process, it is determined the code was introduced into the environment as a result of a compromised laptop being used to harvest credentials and access the organization's code repository. While the laptop itself was not used to access the code repository, an attacker was able to leverage the harvested credentials from another system in the development environment to bypass the ACLs limiting access to the repositories. Which of the following controls MOST likely would have interrupted the kill chain in this attack?
(Multiple Choice)
4.8/5  (40)
(40)
A security engineer is analyzing an application during a security assessment to ensure it is configured to protect against common threats. Given the output below: 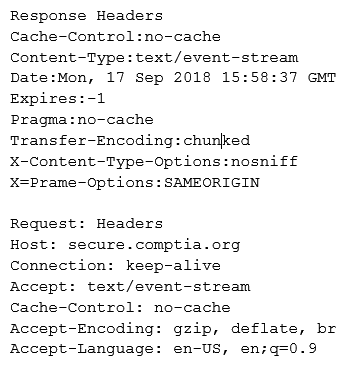 Which of the following tools did the security engineer MOST likely use to generate this output?
Which of the following tools did the security engineer MOST likely use to generate this output?
(Multiple Choice)
4.8/5  (27)
(27)
A Chief Information Security Officer (CISO) has created a survey that will be distributed to managers of mission-critical functions across the organization. The survey requires the managers to determine how long their respective units can operate in the event of an extended IT outage before the organization suffers monetary losses from the outage. To which of the following is the survey question related? (Choose two.)
(Multiple Choice)
4.8/5  (30)
(30)
A government organization operates and maintains several ICS environments. The categorization of one of the ICS environments led to a moderate baseline. The organization has complied a set of applicable security controls based on this categorization. Given that this is a unique environment, which of the following should the organization do NEXT to determine if other security controls should be considered?
(Multiple Choice)
4.7/5  (42)
(42)
During a recent incident, sensitive data was disclosed and subsequently destroyed through a properly secured, cloud-based storage platform. An incident response technician is working with management to develop an after action report that conveys critical metrics regarding the incident. Which of the following would be MOST important to senior leadership to determine the impact of the breach?
(Multiple Choice)
4.8/5  (43)
(43)
A business is growing and starting to branch out into other locations. In anticipation of opening an office in a different country, the Chief Information Security Officer (CISO) and legal team agree they need to meet the following criteria regarding data to open the new office: Store taxation-related documents for five years Store customer addresses in an encrypted format Destroy customer information after one year Keep data only in the customer's home country Which of the following should the CISO implement to BEST meet these requirements? (Choose three.)
(Multiple Choice)
4.8/5  (28)
(28)
An organization is preparing to develop a business continuity plan. The organization is required to meet regulatory requirements relating to confidentiality and availability, which are well-defined. Management has expressed concern following initial meetings that the organization is not fully aware of the requirements associated with the regulations. Which of the following would be MOST appropriate for the project manager to solicit additional resources for during this phase of the project?
(Multiple Choice)
4.8/5  (28)
(28)
A security administrator wants to implement controls to harden company-owned mobile devices. Company policy specifies the following requirements: Mandatory access control must be enforced by the OS. Devices must only use the mobile carrier data transport. Which of the following controls should the security administrator implement? (Choose three.)
(Multiple Choice)
4.8/5  (39)
(39)
A Chief Information Security Officer (CISO) is reviewing the controls in place to support the organization's vulnerability management program. The CISO finds patching and vulnerability scanning policies and procedures are in place. However, the CISO is concerned the organization is siloed and is not maintaining awareness of new risks to the organization. The CISO determines systems administrators need to participate in industry security events. Which of the following is the CISO looking to improve?
(Multiple Choice)
4.9/5  (33)
(33)
A security administrator is updating corporate policies to respond to an incident involving collusion between two systems administrators that went undetected for more than six months. Which of the following policies would have MOST likely uncovered the collusion sooner? (Choose two.)
(Multiple Choice)
4.9/5  (31)
(31)
A company has created a policy to allow employees to use their personally owned devices. The Chief Information Security Officer (CISO) is getting reports of company data appearing on unapproved forums and an increase in theft of personal electronic devices. Which of the following security controls would BEST reduce the risk of exposure?
(Multiple Choice)
4.8/5  (34)
(34)
A developer emails the following output to a security administrator for review: 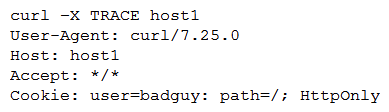 Which of the following tools might the security administrator use to perform further security assessment of this issue?
Which of the following tools might the security administrator use to perform further security assessment of this issue?
(Multiple Choice)
4.7/5  (34)
(34)
An organization is concerned that its hosted web servers are not running the most updated version of software. Which of the following would work BEST to help identify potential vulnerabilities?
(Multiple Choice)
4.9/5  (34)
(34)
A manufacturing company recently recovered from an attack on its ICS devices. It has since reduced the attack surface by isolating the affected components. The company now wants to implement detection capabilities. It is considering a system that is based on machine learning. Which of the following features would BEST describe the driver to adopt such nascent technology over mainstream commercial IDSs?
(Multiple Choice)
4.9/5  (40)
(40)
An internal application has been developed to increase the efficiency of an operational process of a global manufacturer. New code was implemented to fix a security bug, but it has caused operations to halt. The executive team has decided fixing the security bug is less important than continuing operations. Which of the following would BEST support immediate rollback of the failed fix? (Choose two.)
(Multiple Choice)
5.0/5  (39)
(39)
Ann, a member of the finance department at a large corporation, has submitted a suspicious email she received to the information security team. The team was not expecting an email from Ann, and it contains a PDF file inside a ZIP compressed archive. The information security learn is not sure which files were opened. A security team member uses an air-gapped PC to open the ZIP and PDF, and it appears to be a social engineering attempt to deliver an exploit. Which of the following would provide greater insight on the potential impact of this attempted attack?
(Multiple Choice)
4.8/5  (27)
(27)
The Chief Executive Officer (CEO) of a small company decides to use cloud computing to host critical corporate data for protection from natural disasters. The recommended solution is to adopt the public cloud for its cost savings. If the CEO insists on adopting the public cloud model, which of the following would be the BEST advice?
(Multiple Choice)
4.9/5  (28)
(28)
Showing 261 - 280 of 442
Filters
- Essay(0)
- Multiple Choice(0)
- Short Answer(0)
- True False(0)
- Matching(0)