Exam 3: CompTIA Advanced Security Practitioner (CASP+) CAS-003
Exam 1: CompTIA A+ Certification Exam: Core 1471 Questions
Exam 2: CompTIA A+ Certification Exam: Core 2409 Questions
Exam 3: CompTIA Advanced Security Practitioner (CASP+) CAS-003442 Questions
Exam 4: CompTIA Advanced Security Practitioner (CASP+) CAS-004107 Questions
Exam 5: CompTIA Cloud Essentials+165 Questions
Exam 6: CompTIA CySA+ Certification Exam (CS0-002)294 Questions
Exam 7: CompTIA Cloud+ (CV0-002)48 Questions
Exam 8: CompTIA Cloud+67 Questions
Exam 9: CompTIA IT Fundamentals387 Questions
Exam 10: CompTIA Network+829 Questions
Exam 11: CompTIA Project+540 Questions
Exam 12: CompTIA PenTest+ Certification Exam165 Questions
Exam 13: CompTIA Server+66 Questions
Exam 14: CompTIA Server+ Certification Exam779 Questions
Exam 15: CompTIA Security+1 k+ Questions
Exam 16: CompTIA Security+ 2021129 Questions
Exam 17: CompTIA CTT+ Essentials378 Questions
Exam 18: CompTIA Linux+252 Questions
Select questions type
A product manager is concerned about the unintentional sharing of the company's intellectual property through employees' use of social media. Which of the following would BEST mitigate this risk?
(Multiple Choice)
4.8/5  (34)
(34)
Management is reviewing the results of a recent risk assessment of the organization's policies and procedures. During the risk assessment it is determined that procedures associated with background checks have not been effectively implemented. In response to this risk, the organization elects to revise policies and procedures related to background checks and use a third-party to perform background checks on all new employees. Which of the following risk management strategies has the organization employed?
(Multiple Choice)
4.9/5  (44)
(44)
First responders, who are part of a core incident response team, have been working to contain an outbreak of ransomware that also led to data loss in a rush to isolate the three hosts that were calling out to the NAS to encrypt whole directories, the hosts were shut down immediately without investigation and then isolated. Which of the following were missed? (Choose two.)
(Multiple Choice)
4.9/5  (43)
(43)
The Chief Information Security Officer (CISO) has asked the security team to determine whether the organization is susceptible to a zero-day exploit utilized in the banking industry and whether attribution is possible. The CISO has asked what process would be utilized to gather the information, and then wants to apply signatureless controls to stop these kinds of attacks in the future. Which of the following are the MOST appropriate ordered steps to take to meet the CISO's request?
(Multiple Choice)
4.9/5  (33)
(33)
The Chief Information Officer (CIO) wants to increase security and accessibility among the organization's cloud SaaS applications. The applications are configured to use passwords, and two-factor authentication is not provided natively. Which of the following would BEST address the CIO's concerns?
(Multiple Choice)
4.8/5  (32)
(32)
A vendor develops a mobile application for global customers. The mobile application supports advanced encryption of data between the source (the mobile device) and the destination (the organization's ERP system). As part of the vendor's compliance program, which of the following would be important to take into account?
(Multiple Choice)
4.9/5  (34)
(34)
An organization's network engineering team recently deployed a new software encryption solution to ensure the confidentiality of data at rest, which was found to add 300ms of latency to data read-write requests in storage, impacting business operations. Which of the following alternative approaches would BEST address performance requirements while meeting the intended security objective?
(Multiple Choice)
5.0/5  (31)
(31)
A penetration testing manager is contributing to an RFP for the purchase of a new platform. The manager has provided the following requirements: Must be able to MITM web-based protocols Must be able to find common misconfigurations and security holes Which of the following types of testing should be included in the testing platform? (Choose two.)
(Multiple Choice)
4.7/5  (32)
(32)
A breach was caused by an insider threat in which customer PII was compromised. Following the breach, a lead security analyst is asked to determine which vulnerabilities the attacker used to access company resources. Which of the following should the analyst use to remediate the vulnerabilities?
(Multiple Choice)
4.7/5  (32)
(32)
An organization wants to arm its cybersecurity defensive suite automatically with intelligence on zero-day threats shortly after they emerge. Acquiring tools and services that support which of the following data standards would BEST enable the organization to meet this objective?
(Multiple Choice)
4.9/5  (39)
(39)
The Chief Information Security Officer (CISO) of an e-retailer, which has an established security department, identifies a customer who has been using a fraudulent credit card. The CISO calls the local authorities, and when they arrive on-site, the authorities ask a security engineer to create a point-in-time copy of the running database in their presence. This is an example of:
(Multiple Choice)
4.8/5  (23)
(23)
A company is migrating systems from an on-premises facility to a third-party managed datacenter. For continuity of operations and business agility, remote access to all hardware platforms must be available at all times. Access controls need to be very robust and provide an audit trail. Which of the following security controls will meet the company's objectives? (Choose two.)
(Multiple Choice)
4.8/5  (38)
(38)
As a result of an acquisition, a new development team is being integrated into the company. The development team has BYOD laptops with IDEs installed, build servers, and code repositories that utilize SaaS. To have the team up and running effectively, a separate Internet connection has been procured. A stand up has identified the following additional requirements: 1. Reuse of the existing network infrastructure 2. Acceptable use policies to be enforced 3. Protection of sensitive files 4. Access to the corporate applications Which of the following solution components should be deployed to BEST meet the requirements? (Select three.)
(Multiple Choice)
4.9/5  (31)
(31)
A forensic analyst suspects that a buffer overflow exists in a kernel module. The analyst executes the following command: 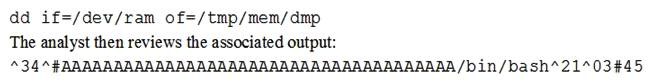 However, the analyst is unable to find any evidence of the running shell. Which of the following of the MOST likely reason the analyst cannot find a process ID for the shell?
However, the analyst is unable to find any evidence of the running shell. Which of the following of the MOST likely reason the analyst cannot find a process ID for the shell?
(Multiple Choice)
4.9/5  (38)
(38)
A security analyst is classifying data based on input from data owners and other stakeholders. The analyst has identified three data types: Financially sensitive data Project data Sensitive project data The analyst proposes that the data be protected in two major groups, with further access control separating the financially sensitive data from the sensitive project data. The normal project data will be stored in a separate, less secure location. Some stakeholders are concerned about the recommended approach and insist that commingling data from different sensitive projects would leave them vulnerable to industrial espionage. Which of the following is the BEST course of action for the analyst to recommend?
(Multiple Choice)
4.9/5  (20)
(20)
A company has decided to lower costs by conducting an internal assessment on specific devices and various internal and external subnets. The assessment will be done during regular office hours, but it must not affect any production servers. Which of the following would MOST likely be used to complete the assessment? (Choose two.)
(Multiple Choice)
4.8/5  (42)
(42)
An electric car company hires an IT consulting company to improve the cybersecurity of its vehicles. Which of the following should achieve the BEST long-term result for the company?
(Multiple Choice)
4.8/5  (42)
(42)
A systems administrator has deployed the latest patches for Windows-based machines. However, the users on the network are experiencing exploits from various threat actors, which the patches should have corrected. Which of the following is the MOST likely scenario?
(Multiple Choice)
4.8/5  (31)
(31)
A newly hired Chief Information Security Officer (CISO) is reviewing the organization's security budget from the previous year. The CISO notices $100,000 worth of fines were paid for not properly encrypting outbound email messages. The CISO expects next year's costs associated with fines to double and the volume of messages to increase by 100%. The organization sent out approximately 25,000 messages per year over the last three years. Given the table below: 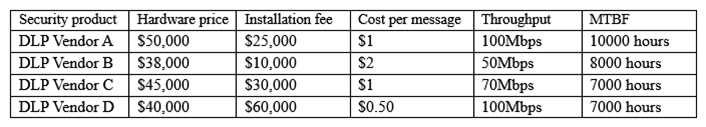 Which of the following would be BEST for the CISO to include in this year's budget?
Which of the following would be BEST for the CISO to include in this year's budget?
(Multiple Choice)
4.9/5  (31)
(31)
A penetration test is being scoped for a set of web services with API endpoints. The APIs will be hosted on existing web application servers. Some of the new APIs will be available to unauthenticated users, but some will only be available to authenticated users. Which of the following tools or activities would the penetration tester MOST likely use or do during the engagement? (Choose two.)
(Multiple Choice)
4.9/5  (46)
(46)
Showing 281 - 300 of 442
Filters
- Essay(0)
- Multiple Choice(0)
- Short Answer(0)
- True False(0)
- Matching(0)