Exam 3: CompTIA Advanced Security Practitioner (CASP+) CAS-003
Exam 1: CompTIA A+ Certification Exam: Core 1471 Questions
Exam 2: CompTIA A+ Certification Exam: Core 2409 Questions
Exam 3: CompTIA Advanced Security Practitioner (CASP+) CAS-003442 Questions
Exam 4: CompTIA Advanced Security Practitioner (CASP+) CAS-004107 Questions
Exam 5: CompTIA Cloud Essentials+165 Questions
Exam 6: CompTIA CySA+ Certification Exam (CS0-002)294 Questions
Exam 7: CompTIA Cloud+ (CV0-002)48 Questions
Exam 8: CompTIA Cloud+67 Questions
Exam 9: CompTIA IT Fundamentals387 Questions
Exam 10: CompTIA Network+829 Questions
Exam 11: CompTIA Project+540 Questions
Exam 12: CompTIA PenTest+ Certification Exam165 Questions
Exam 13: CompTIA Server+66 Questions
Exam 14: CompTIA Server+ Certification Exam779 Questions
Exam 15: CompTIA Security+1 k+ Questions
Exam 16: CompTIA Security+ 2021129 Questions
Exam 17: CompTIA CTT+ Essentials378 Questions
Exam 18: CompTIA Linux+252 Questions
Select questions type
The Chief Executive Officer (CEO) of a small startup company has an urgent need for a security policy and assessment to address governance, risk management, and compliance. The company has a resource-constrained IT department, but has no information security staff. The CEO has asked for this to be completed in three months. Which of the following would be the MOST cost-effective solution to meet the company's needs?
(Multiple Choice)
4.8/5  (42)
(42)
During a sprint, developers are responsible for ensuring the expected outcome of a change is thoroughly evaluated for any security impacts. Any impacts must be reported to the team lead. Before changes are made to the source code, which of the following MUST be performed to provide the required information to the team lead?
(Multiple Choice)
4.7/5  (36)
(36)
A school contracts with a vendor to devise a solution that will enable the school library to lend out tablet computers to students while on site. The tablets must adhere to string security and privacy practices. The school's key requirements are to: Maintain privacy of students in case of loss Have a theft detection control in place Be compliant with defined disability requirements Have a four-hour minimum battery life Which of the following should be configured to BEST meet the requirements? (Choose two.)
(Multiple Choice)
4.8/5  (33)
(33)
A security administrator is updating a company's SCADA authentication system with a new application. To ensure interoperability between the legacy system and the new application, which of the following stakeholders should be involved in the configuration process before deployment? (Choose two.)
(Multiple Choice)
4.9/5  (36)
(36)
A company recently implemented a variety of security services to detect various types of traffic that pose a threat to the company. The following services were enabled within the network: • Scan of specific subsets for vulnerabilities • Categorizing and logging of website traffic • Enabling specific ACLs based on application traffic • Sending suspicious files to a third-party site for validation A report was sent to the security team that identified multiple incidents of users sharing large amounts of data from an on-premise server to a public site. A small percentage of that data also contained malware and spyware Which of the following services MOST likely identified the behavior and sent the report?
(Multiple Choice)
4.7/5  (32)
(32)
An organization is currently working with a client to migrate data between a legacy ERP system and a cloud-based ERP tool using a global PaaS provider. As part of the engagement, the organization is performing data deduplication and sanitization of client data to ensure compliance with regulatory requirements. Which of the following is the MOST likely reason for the need to sanitize the client data? (Choose two.)
(Multiple Choice)
4.9/5  (26)
(26)
A security administrator is advocating for enforcement of a new policy that would require employers with privileged access accounts to undergo periodic inspections and review of certain job performance data. To which of the following policies is the security administrator MOST likely referring?
(Multiple Choice)
4.9/5  (37)
(37)
A Chief Information Security Officer (CISO) requests the following external hosted services be scanned for malware, unsecured PII, and healthcare data: Corporate intranet site Online storage application Email and collaboration suite Security policy also is updated to allow the security team to scan and detect any bulk downloads of corporate data from the company's intranet and online storage site. Which of the following is needed to comply with the corporate security policy and the CISO's request?
(Multiple Choice)
5.0/5  (38)
(38)
A security analyst, who is working in a Windows environment, has noticed a significant amount of IPv6 traffic originating from a client, even though IPv6 is not currently in use. The client is a stand-alone device, not connected to the AD that manages a series of SCADA devices used for manufacturing. Which of the following is the appropriate command to disable the client's IPv6 stack?
(Multiple Choice)
4.7/5  (30)
(30)
An SQL database is no longer accessible online due to a recent security breach. An investigation reveals that unauthorized access to the database was possible due to an SQL injection vulnerability. To prevent this type of breach in the future, which of the following security controls should be put in place before bringing the database back online? (Choose two.)
(Multiple Choice)
4.8/5  (38)
(38)
A company wants to implement a cloud-based security solution that will sinkhole malicious DNS requests. The security administrator has implemented technical controls to direct DNS requests to the cloud servers but wants to extend the solution to all managed and unmanaged endpoints that may have user-defined DNS manual settings. Which of the following should the security administrator implement to ensure the solution will protect all connected devices?
(Multiple Choice)
4.7/5  (25)
(25)
After analyzing code, two developers at a company bring these samples to the security operations manager: 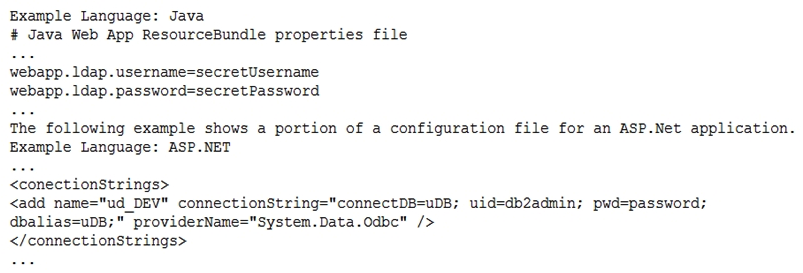 Which of the following would BEST solve these coding problems?
Which of the following would BEST solve these coding problems?
(Multiple Choice)
4.7/5  (38)
(38)
A company contracts a security consultant to perform a remote white-box penetration test. The company wants the consultant to focus on Internet-facing services without negatively impacting production services. Which of the following is the consultant MOST likely to use to identify the company's attack surface? (Choose two.)
(Multiple Choice)
4.9/5  (31)
(31)
A project manager is working with a software development group to collect and evaluate user stories related to the organization's internally designed CRM tool. After defining requirements, the project manager would like to validate the developer's interpretation and understanding of the user's request. Which of the following would BEST support this objective?
(Multiple Choice)
4.8/5  (29)
(29)
An organization has employed the services of an auditing firm to perform a gap assessment in preparation for an upcoming audit. As part of the gap assessment, the auditor supporting the assessment recommends the organization engage with other industry partners to share information about emerging attacks to organizations in the industry in which the organization functions. Which of the following types of information could be drawn from such participation?
(Multiple Choice)
5.0/5  (32)
(32)
A new cluster of virtual servers has been set up in a lab environment and must be audited before being allowed on the production network. The security manager needs to ensure unnecessary services are disabled and all system accounts are using strong credentials. Which of the following tools should be used? (Choose two.)
(Multiple Choice)
4.8/5  (35)
(35)
After embracing a BYOD policy, a company is faced with new security challenges from unmanaged mobile devices and laptops. The company's IT department has seen a large number of the following incidents: Duplicate IP addresses Rogue network devices Infected systems probing the company's network Which of the following should be implemented to remediate the above issues? (Choose two.)
(Multiple Choice)
5.0/5  (26)
(26)
A security engineer is assessing a new IoT product. The product interfaces with the ODBII port of a vehicle and uses a Bluetooth connection to relay data to an onboard data logger located in the vehicle. The data logger can only transfer data over a custom USB cable. The engineer suspects a replay attack is possible against the cryptographic implementation used to secure messages between segments of the system. Which of the following tools should the engineer use to confirm the analysis?
(Multiple Choice)
4.7/5  (39)
(39)
As part of the development process for a new system, the organization plans to perform requirements analysis and risk assessment. The new system will replace a legacy system, which the organization has used to perform data analytics. Which of the following is MOST likely to be part of the activities conducted by management during this phase of the project?
(Multiple Choice)
4.8/5  (25)
(25)
A company has completed the implementation of technical and management controls as required by its adopted security policies and standards. The implementation took two years and consumed all the budget approved to security projects. The board has denied any further requests for additional budget. Which of the following should the company do to address the residual risk?
(Multiple Choice)
4.8/5  (30)
(30)
Showing 401 - 420 of 442
Filters
- Essay(0)
- Multiple Choice(0)
- Short Answer(0)
- True False(0)
- Matching(0)